Frequently Asked Questions
The Network to Network for the Gulf of Mexico (N2N-GoM) is a means to bring together the more than 181 GoM networks that exist across market sectors, academia, and government.
The concept emerged from the convergence of multiple interests shared by a binational interdisciplinary team of academic, industrial, government and community-based leaders from U.S. and Mexico, who realized that by leveraging the power of their network collaborations through team science, it was possible to integrate all available scientific evidence from the GoM (including data from field and laboratory observations, model predictions, and experts’ knowledge), share knowledge and operational infrastructure; and build research, academic, service, and entrepreneurship capacity around the Gulf of Mexico.
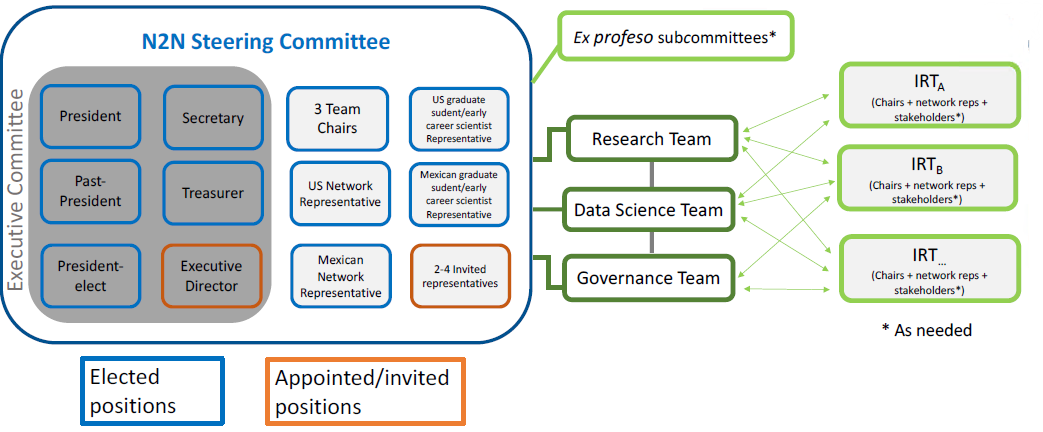
Executive Committee, Working Teams, Integrated Research Teams.
As of today, N2N-GoM has come as far as it has thanks to the sponsorship of the NSF-AccelNet Program, and to the co-sponsoring of multiple networks including the Yucatan Initiative, the Society for Underwater Technology in the U.S., the Harte Research Institute for Gulf of Mexico Studies, and Texas A&M University.
Through a team science approach, the specific IRTs launched in the following months will expedite the development of products and services addressing specific themes based on the variables and processes defined in the Bayesian Network Risk Assessment Model. These will press the Working Teams to produce the Decadal Research Agenda for the GoM, the Governance of the N2N-GoM Non-Profit Organization, and the Business Model based on Data Science that can make it sustainable, by becoming the decision-making risk-driven Organization in the GoM to go to the point of reference Organization to acquire information to improve decision-making for any entity vested in the GoM.
The risk methodology used is based on a risk theory inspired by the United Nations Disaster Relief Office (UNDRO, 1980). This theory introduces the concept of Risk Assessment as a state for a given spatial and time domain.
Risk = Hazard x Vulnerability x Consequences (eq. 1) where Risk = P(T)x P(C/T)x u(C) (eq.1)
In equation 1, P(T) is the Hazard or probability of a given threat intensity (T), P(C|T) is the Vulnerability or conditional probability of experimenting with a consequence or damage level (C) given likely threat intensities (T).


